NIST Guidelines for Password Security: Using a Password Manager
NIST Guidelines for Password Security: If You Are Using a Password Manager, You Should Be in Good Shape
The US National Institute of Standards and Technology (NIST) is a federal agency that is part of the US Department of Commerce which means that although it doesn't have any regulatory functions, it employs plenty of people that are supposed to know what they're talking about. For years, NIST has discussed, among other things, the problem of secure online authentication and passwords. As the organization's name suggests, its goal is to standardize the world of technology, and although it hasn't completely unified everyone's perception, its guidelines have, to a certain extent, influenced our ideas on what is and what isn't a good password.
Should we continue to listen to everything it says about online authentication?
NIST's password guidelines have been less than perfect
There's a good chance that you've recently faced the challenge of creating what many would say is a strong password. We're talking about a long (think more than 12 characters) password that contains uppercase and lowercase letters, digits, and special characters. We've discussedtime and again how frustrating this could be, especially when the password requirements aren't as clear as they should be. We reckon that we don't even need to mention the problem of remembering the complex jumble of letters, numbers, and special characters.
Yet, in 2003, NIST said that this is the only secure way to create a password, and vendors started trying to force people to follow it, something that is continuing to this day. There is no standard. Every developer decides for themselves how complex users' passwords will be, but it's fair to say that pretty much everyone has some requirements. The results? Well, the whole push for more complex passwords has made the task of managing them next to impossible.
Users have been trying to work their way around the requirements. Some just add a "123!@" to the end of "Password" which defeats the purpose of requiring numbers and special characters altogether. Others write them down on sticky notes, stick them to their monitors, and eventually lose them. For most, however, the solution is clear – create one or two reasonably complex passwords and use them for multiple accounts.
All in all, the inconvenience caused by NIST's old password guidelines has been huge, and the benefit has been questionable. That's why, about a year and a half ago, NIST replaced them with new ones.
NIST had a change of heart
We can only imagine that the whole thing was somewhat embarrassing. Bill Burr, one of the authors of NIST's 2003 guidelines, even apologized for putting people through all this frustration. The thing is, his old advice was clearly backfiring, and something had to be done.
In the summer of 2017, a different team of experts published NIST's new password guidelines. The Institute is now putting less emphasis on complexity and is instead focusing on length. According to the document (due to the US Government Shutdown, the resource is unavailable at the time of writing, but you can find an archived version here), "Password length has been found to be the primary factor in characterizing password strength." It then states that although introducing additional sets of characters makes a password more complex and therefore theoretically harder to guess, the predictability with which users react to this type of requirement (i.e. "Password123!@") decreases its impact on the overall password security.
NIST's current advice to vendors is to set a minimum password length requirement which should be based on the threat model. Websites and apps should also set their maximum length limit at no less than 64 symbols, and they should allow all types of characters (including spaces) in the password.
Instead of trying to encourage users to create good passwords (which clearly didn't work the last time around), the Institute is now trying to persuade them to avoid bad ones. NIST's document says that vendors should forbid easy-to-guess dictionary words and even suggests that they should check the password the user is trying to create against a database of passwords that have already been leaked during data breaches. After NIST released its guidelines, Troy Hunt, the operator of the famous HaveIBeenPwned service, set up a free tool that can perform this type of check against hundreds of millions of exposed passwords.
One of the more controversial points in NIST's latest password guidance states that password expiration policies should be abolished completely. The Institute's experts think that if there's no reason to believe that a password has been compromised in any way, there's no reason to change it, even if it is several years old. Not everyone agrees with this point of view, but then again, the logic behind it is crystal clear: users are unwilling to remember a brand new password (which, ideally, is long and complex enough) every few months, which is why they just put a "1" or a "2" to the end of their old one. If employers and vendors decide to heed this particular advice, they will make password management just a tiny bit less of a chore. And this brings us to a very important conclusion.
Even with NIST's new guidelines, users are still going to have a hard time
The new rules make the tedious task of securely managing passwords easier. They don't make it easy, though, and that's a rather crucial thing.
The advice about creating long passphrases instead of shorter, but more complex passwords has its roots in a rather famous webcomic by XKCD. You can't argue with the fact that it makes a great deal of sense: math says that "correcthorsebatterystaple" has higher entropy than "Tr0ub4dor&3", and there's no doubt that it's easier to remember. The thing is, nowadays, you have dozens, if not hundreds of online accounts, and if you want to avoid password reuse, and you do, you need to remember dozens if not hundreds of random four-word combinations. For most people, this is a tall order.
In fact, it's fair to say that without additional help, managing a large number of passphrases is more or less just as hard as managing a large number of passwords. The only reasonable solution, then, is a password manager.
Using a Password Manager
A password manager stores and encrypts your login credentials as well as other sensitive information in one central vault, and it lets you use it at any time by entering just one master password. Password managers lets you use strong, unique passwords for all your accounts.
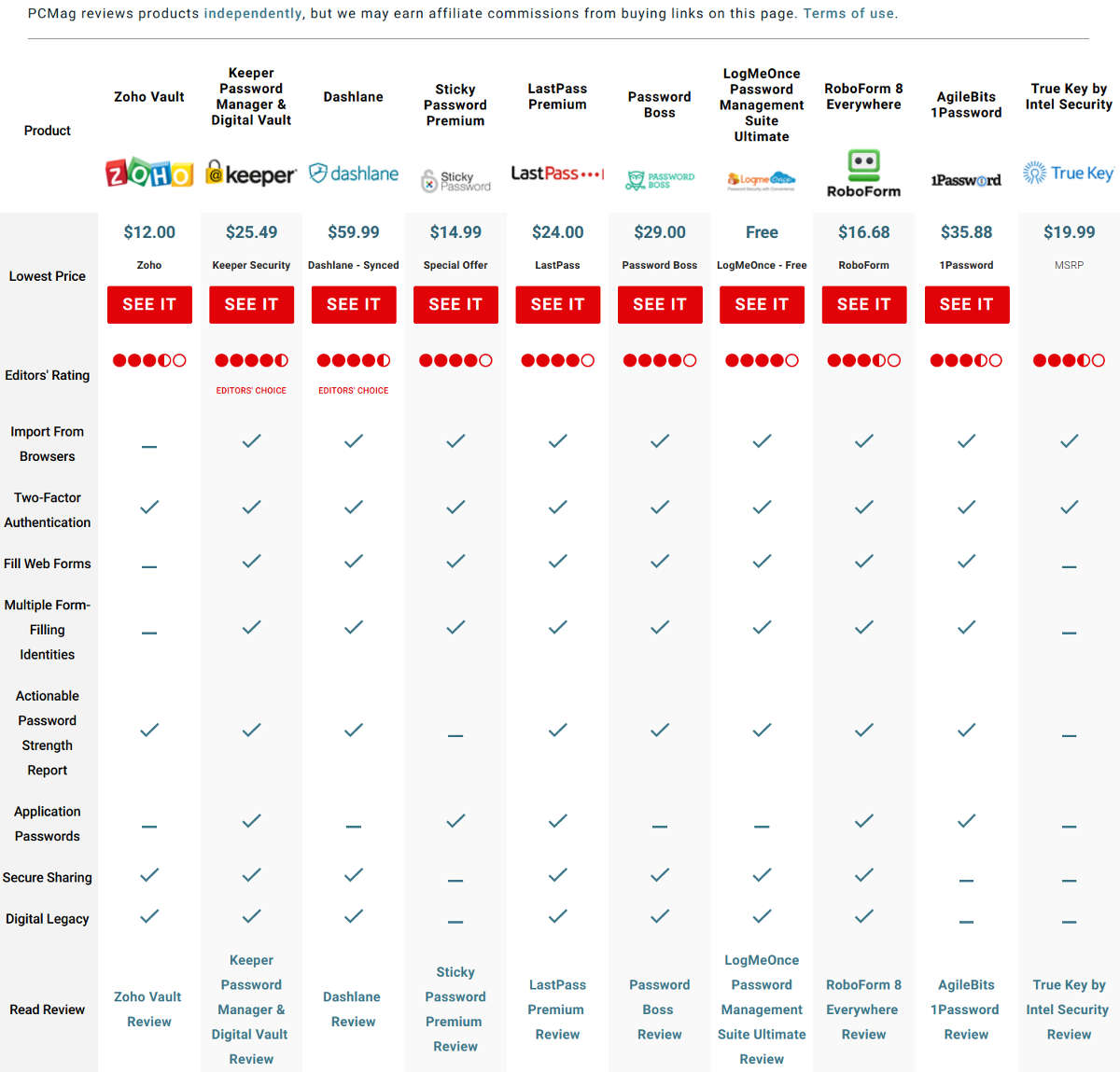
The Best Password Managers for 2019